We use cookies (or similar technologies) to collect information about how you interact with our website and allow us to remember you. We use this to improve your experience and for analytics about who our visitors are. To learn more, see our Privacy policy
Everything Set: why we do what we do
We’ve spoken a lot about what we do: we’ve spoken about our AI, our data engineering, and the monitoring of device behaviors and data patterns which allow us to accurately alert users to unusual data activity and make sure their devices are only doing what they’re supposed to. But we haven’t yet spoken about why we do what we do.
This is that.
Smart devices
Smart devices are fantastic. They streamline arduous activities, take care of the little things we never knew we could forget about, and enhance everyday activities: they automate and update and remind. They inform. They keep track. They do what we’re too busy to do. They monitor. We exist inside a network of usefulness.
Our ever-growing list of smart devices constantly communicates streams of information: our interests and activities, our favorite TV shows, the layout of our homes, our medical conditions, the color of our lightbulbs, the location of our children, the temperature of our bedrooms…
When empty, our smart homes are still bristling with life: pings and whispers of data moving from one room to another; carrying conversations with the cloud so you can access your home remotely, from work or a coffee shop or across the country; digital creaks in floorboards during the night as data never sleeps.
Combined, through constant access, our devices paint portraits of our lives.
This technological evolution is astonishing. It’s fantastic. Accessibility can transform lives. But with this network of usefulness comes a new human vulnerability: a lack of privacy and safety behind locked doors.
A new human vulnerability
It sounds cold and strange: smart device privacy and safety. Device behavior, and the resulting data, is something intangible that, for most people, is an inevitable, unavoidable part of having a phone they can text from.
It’s just the thing that makes the stuff work.
And for most people that’s all they need to know about how things work: Device A talks to Device B and a 3D model of Gandalf starts its 16-hour print time. Lovely.
But these device conversations have potential vulnerabilities. Someone halfway around the world could learn about your proclivity for Lord of the Rings or, more pressingly, watch your security footage. Someone could learn your schedule or know when you’re going on holiday. They could know when you’re home and when you’ve popped out to the store…
That’s the small scale.
En masse, our connected world can be leveraged to launch cyberattacks.
We’re not a fan of all that so we thought we’d do something about it.
User privacy and safety
These days there’s a lot of wall building. There are a lot of barriers and obstacles put in place to make access difficult (although not impossible). We didn’t just want to build a wall around your smart devices like some sort of preemptive bandaid. Walls are brutish and inelegant, they’re never built high enough or wide enough, and need to be constantly expanded. More importantly, they don’t put the power in the hands of the user and that’s exactly what we wanted to do.
We wanted to give you all the insight necessary to know your smart devices are only doing what they’re supposed to: that they’re being as parsimonious with your data as we would expect and that you are getting privacy and safety without having to lift a finger.
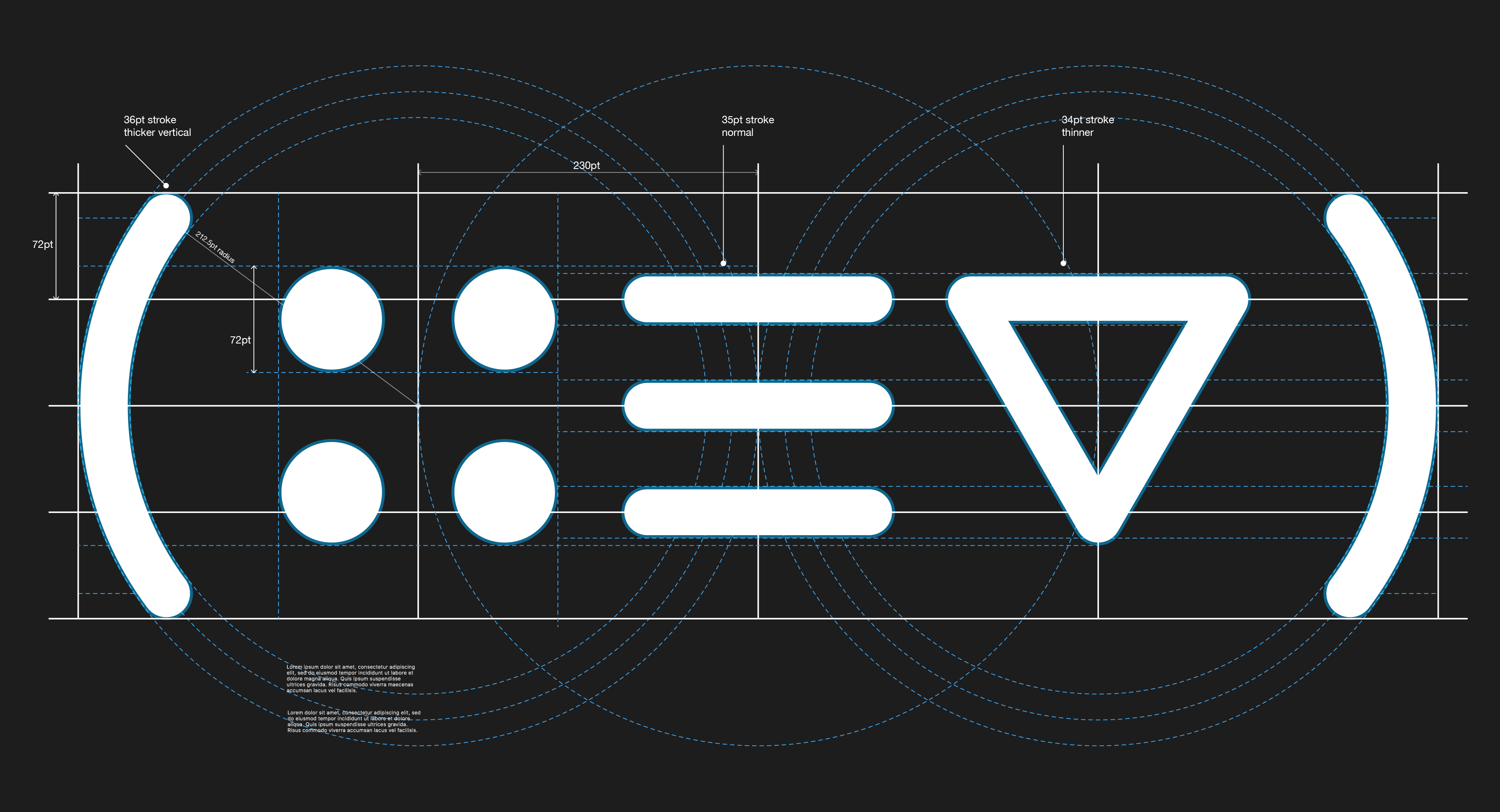
So we built a body: a box, a brain: our analytics engine, and a mouthpiece: our companion app.
Our box plugs into your router and monitors the behaviors and traffic flows of your smart devices and our companion app immediately alerts you if something unusual happens. Then, it either helps you fix the problem or automatically blocks the communication. That’s it! You can completely forget about us until something comes up.
However, if you do have a deeper interest in the activity of your home network, you can monitor all of your smart devices in the app. We provide a suite of information including an ‘Everything Set score’ which gives an overview of how well your devices are behaving and how vulnerable they are at a glance.
So that’s us. That’s why we do what we do.
We’re putting privacy and safety back into the hands of the user.